Despite the reputation of the WordPress Content Management System exceeding all expectations in terms of flawless content publishing and seamless user-access control, there are still some worrying security breaches that need prioritized handling.
Two important access points on a WordPress website should be protected at all costs. The first one is the wp-login.php page responsible for accommodating both normal and privileged users.
[ You might also like: How to Reset WordPress Admin Password via MySQL ]
The second one is the wp-admin/ page responsible for accommodating the admin users of the site. Protecting these two WordPress site pages discourages brute force attacks.
Block Access to wp-admin and wp-login in Apache
Configuring the Apache Web Server environment to communicate with your WordPress site in any capacity first requires access to the host’s main configuration file.
Open your WordPress vhost apache configuration file.
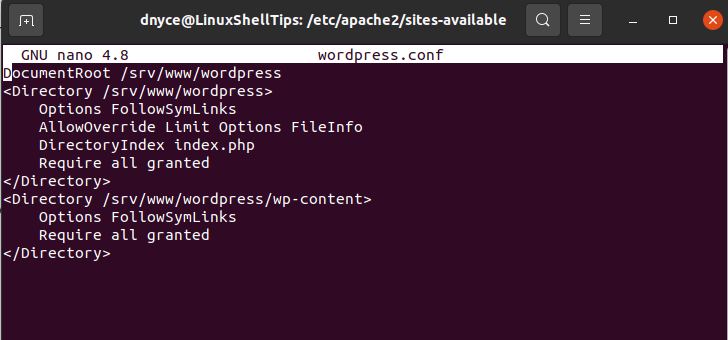
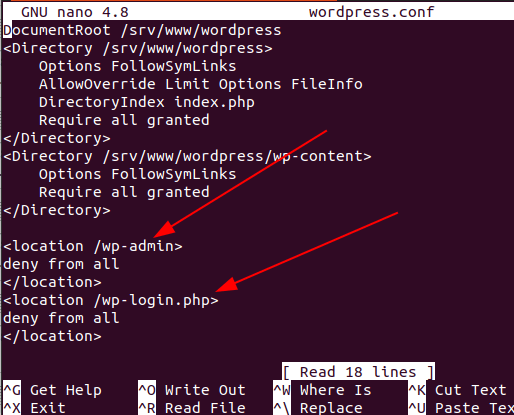
On my end, this is the custom configuration file associated with my WordPress site. We are going to use the <location></location> tags in this file to block access to the wp-admin and wp-login.php WordPress pages.
<location /wp-admin> deny from all </location> <location /wp-login.php> deny from all </location>
Now restart the Apache server.
$ sudo systemctl restart apache2 [On Ubuntu, Debian & Mint] $ sudo systemctl restart httpd [On RHEL/CentOS/Fedora & Rocky Linux/AlmaLinux]
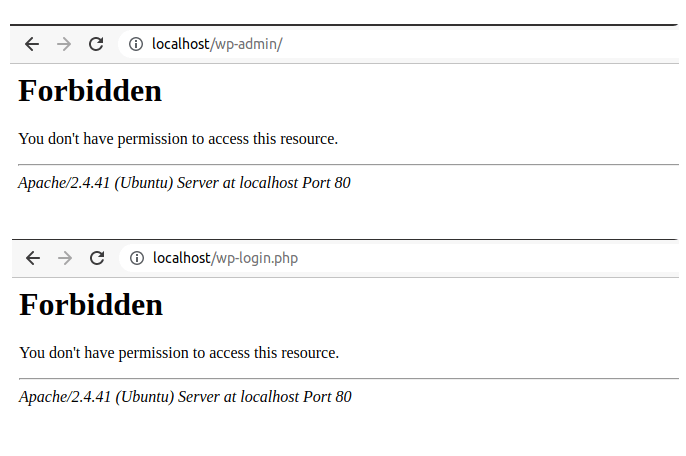
Reloading the page after restarting Apache led to the following display.
Allowing Access to WordPress Admin by IP Address
If you only want to grant yourself access to these two pages, you could specify the IP address you will be using through the allow from clause as demonstrated in the following screen capture.
<location /wp-admin> allow from 127.0.0.1 allow from 192.168.2.9 allow from 10.32.15.7 deny from all </location> <location /wp-login.php> allow from 127.0.0.1 allow from 192.168.2.9 allow from 10.32.15.7 deny from all </location>
Denying Access to WordPress Admin by IP Address
<location /wp-admin> deny from 192.168.2.9 deny from 10.32.15.7 allow from all </location> <location /wp-login.php> deny from 192.168.2.9 deny from 10.32.15.7 allow from all </location>
Make sure to restart the Apache server after making changes to the configuration.
Block Access to wp-admin and wp-login in Nginx
With Nginx, the approach to block user access to wp-admin and wp-login.php WordPress pages is almost similar to Apache’s technique. First, access the related Nginx configuration file for your WordPress site.
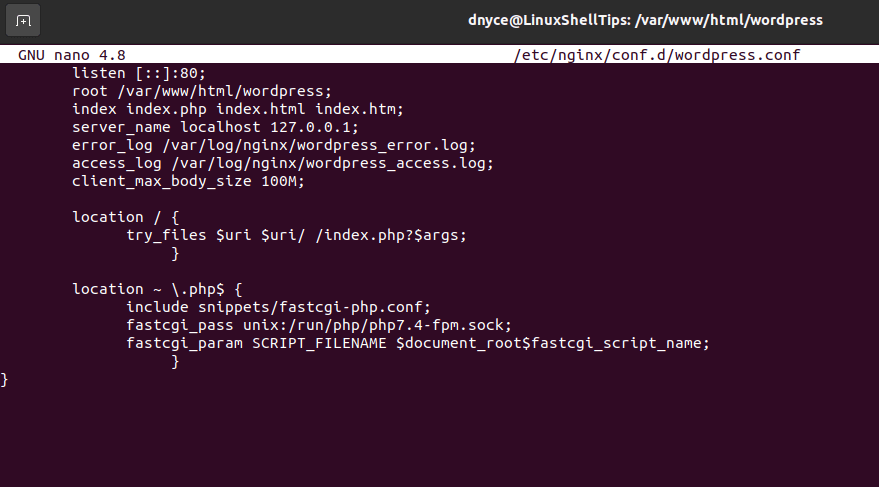
The location tags to use with Nginx have a slightly different syntax as depicted below:
location {
}
To block all access to the two WordPress pages:
location /wp-admin {
deny all;
}
location = /wp-login.php {
deny all;
}
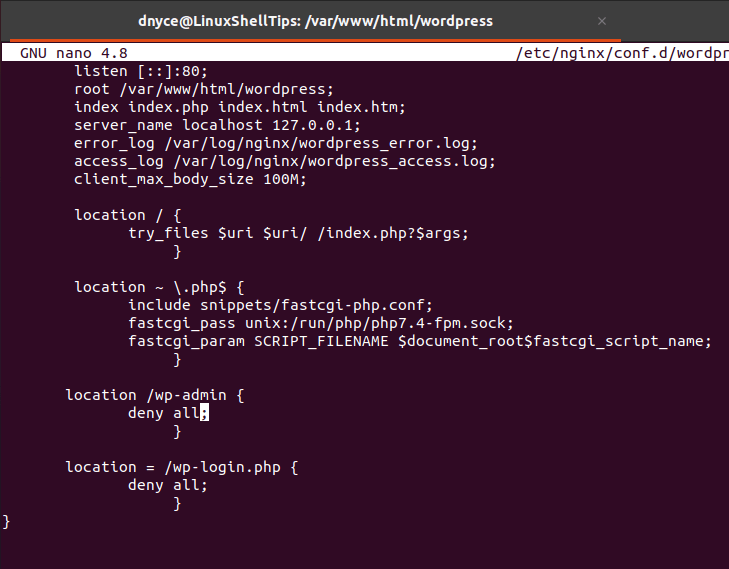
After making changes, restart the Nginx server.
$ sudo systemctl restart nginx
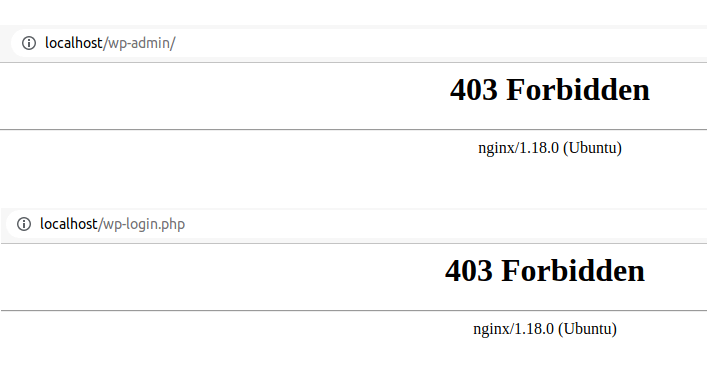
Reloading the page after restarting Nginx led to the following display error.
Restricting Access to WordPress Admin by IP Address
location /wp-admin {
allow 192.168.2.9;
allow 10.32.15.7;
deny all;
}
location = /wp-login.php {
allow 192.168.2.9;
allow 10.32.15.7;
deny all;
}
Blocking Access to WordPress Admin by IP Address
location /wp-admin {
deny 192.168.2.9;
deny 10.32.15.7;
allow all;
}
location = /wp-login.php {
deny 192.168.2.9;
deny 10.32.15.7;
allow all;
}
Make sure to restart the Nginx server after making changes to the configuration.
[ You might also like: How to Block XML-RPC in WordPress Using Nginx/Apache ]
As a WordPress administrator, having the power to decide who has access to what section of your WordPress site saves the site’s reputation from risky users or access that can compromise its integrity and reputation for good.
