Socat or SOcket CAT is a Linux command-line/terminal-based utility used to establish and transfer data between two bidirectional byte streams.
The socat command can be implemented in multiple scenarios because of two main reasons:
- Data sinks and sources; of different types and existing in a large set, can be used to construct streams.
- These constructed streams can be associated with many address options.
The socat command can be likened to the netcat utility which is tied to the TCP and UDP protocols. However, socat has a security advantage (chrooting) over netcat and also supports devices, pipes, files, SSL, client for SOCKS4, TCP sockets, proxy CONNECT, UNIX sockets, etc.
Socat Command in Action
To be more acquainted with this Linux command-line utility, we need to list some of its practical applications. The following bullet points summarize some popular socat utility applications:
- Security testing and research.
- TCP-oriented programs to serial line redirection.
- As UNIX sockets shell interface.
- External socksifier.
- Establishing su and chroot secure environments for executing server/client shell scripts on a shared network connection.
- The logical connection of serial lines on distinct computers.
- IP6 relay.
- Security testing by attacking weak firewalls.
- TCP port forwarding.
Install Socat Utility in Linux
If socat Linux command-line-based utility is not already installed on your Linux operating system distribution, refer to one of the following installation commands in reference to the Linux OS distribution you are using:
$ sudo apt install socat [On Debian, Ubuntu and Mint] $ sudo yum install socat [On RHEL/CentOS/Fedora and Rocky Linux/AlmaLinux] $ sudo emerge -a net-misc/socat [On Gentoo Linux] $ sudo pacman -S socat [On Arch Linux] $ sudo zypper install socat [On OpenSUSE]
As already discussed, socat is a superior alternative to netcat utility because of its powerful and advanced features. We should now be able to see some practical examples of the usage of socat utility via the Linux command line environment.
Its usage syntax is as follows:
# socat [options] <address> <address>
Make sure you have sudoer/root user privileges on your Linux machine.
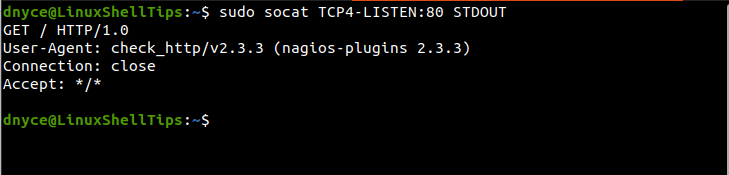
1. Listen On a Specific Port
We can instruct socat to listen on a specific port e.g 80 via the TCP protocol and print out any associated findings via STDOUT as demonstrated below.
$ sudo socat TCP4-LISTEN:80 STDOUT
TCP can switch to other different values such as TCP6, TCP6-LISTEN, and TCP4.
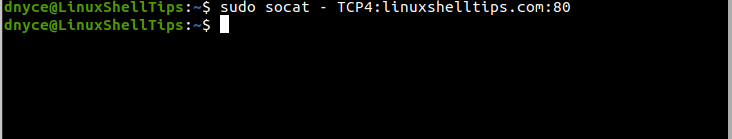
2. Connect to Remote Server on Port
To connect to a server associated with a port, we would run:
$ sudo socat – TCP4:ubuntumint.com:80
3. TCP Port Forwarder
It is also an effective TCP port forwarder. For instance, port 81 connections can be forwarded to port 80 as demonstrated:
For a single connection.
$ sudo socat TCP4-LISTEN:81 TCP4:192.168.122.1:80
For multiple connections.
$ sudo socat TCP4-LISTEN:81,fork,reuseaddr TCP4:TCP4:192.168.122.1:80
You can cancel port forwarding with the keyboard combination [Ctrl]+c.
4. Listening to Local Port
Listening to local port www.
$ sudo socat TCP4-LISTEN:www TCP4:ubuntumint.com:www
5. Listening to Specific Port on Remote Socket
If we wanted to listen to a specific port, accept its connection and forward it to a remote Unix socket e.g mysql.sock, we would implement the socat command in the following manner:
$ sudo socat TCP-LISTEN:3309,reuseaddr,fork UNIX-CONNECT:/var/lib/mysql/mysql.sock
6. Network-based Message Collector
This simple example demonstrates the implementation of a network-based message collector. After client connection to port 3354 is successful, the file /tmp/testing.log appends clients-sent data via a newly generated child process. This file is automatically created by socat when found to be absent.
$ sudo socat -u TCP4-LISTEN:3354,reuseaddr,fork OPEN:/tmp/testing.log,creat,append
With the above-discussed few examples and further reference to the socat manual page, we should be able to explore it to its depth.
$ man socat
